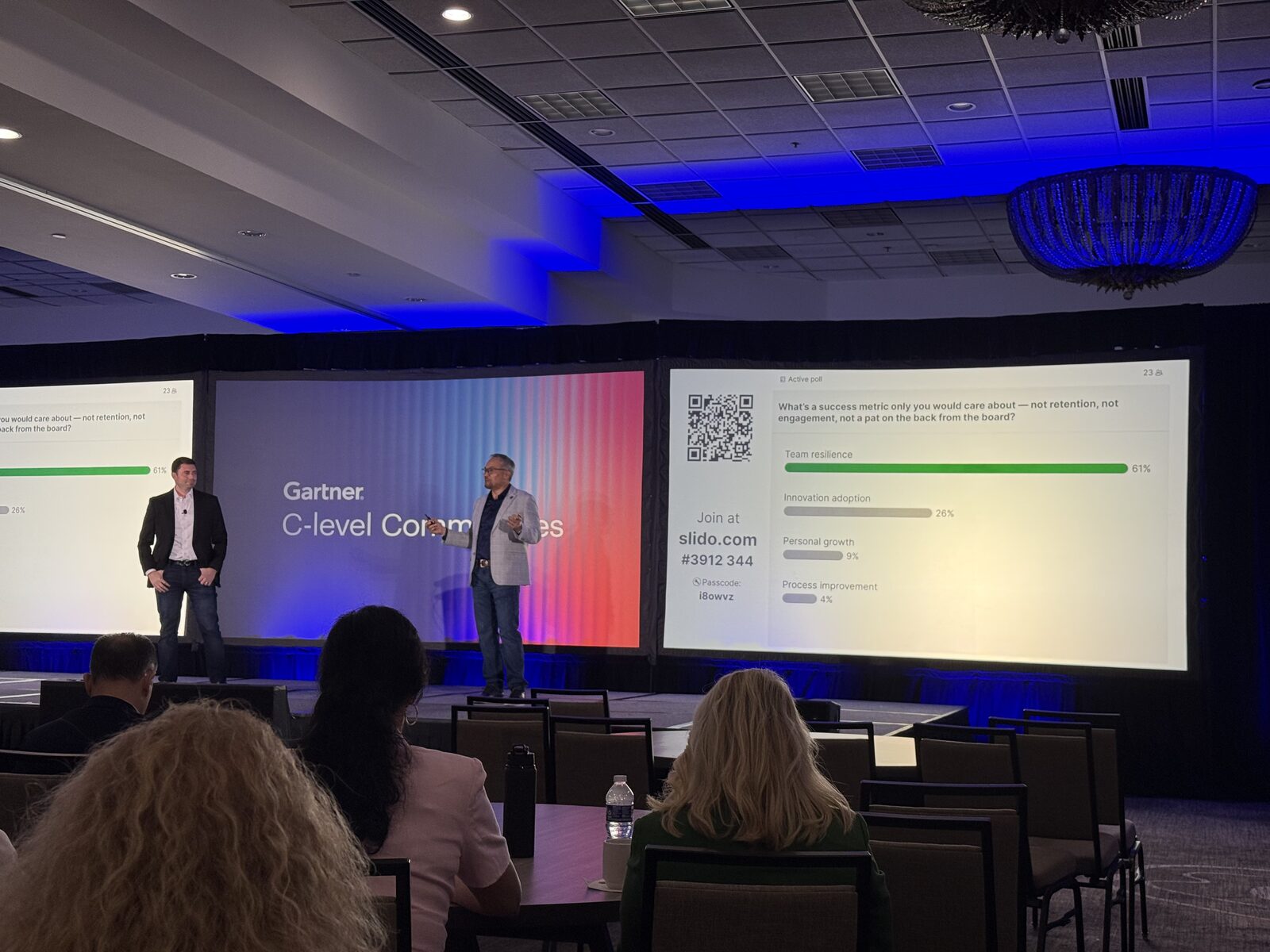
Yesterday at the Florida CIO & CISO Executive Summit, a session on AI in cybersecurity put up a slide titled simply: “AI fights AI.” It’s a real and important framing. The underlying point is true. What kept turning over in my head was the follow-up.
So I raised my hand.
“If the model is AI fights AI, then the side with deeper pockets and more compute wins. That isn’t a vendor problem — it’s a structural problem we all need to solve. What’s the industry’s answer to what I’d call an AI DDoS — Deeper pockets, more Compute? And the deeper question: what about the companies that don’t have those deeper pockets to begin with — how does a mid-market or smaller organization defend against an adversary with mythic-scale capabilities?”
The room got quiet. Nobody had a clean answer — including me. The vendors in the room are smart, the analysts are sharp, the CISOs in the conversation are operating some of the best programs in the country, and none of us had a satisfying response. That, to me, is exactly why the question is worth asking out loud.
This isn’t a critique of any one vendor or any one program. It’s a problem statement for the industry.
The asymmetry we need to talk about collectively
Across every session yesterday — agentic AI security, non-human identity, operational trust — the implicit assumption is that defenders will keep pace with attackers technologically. But pace is a function of capital. The attackers don’t have a CFO asking why the security budget grew 40% year-over-year. We do. And the attackers raise capital on the same AI hype cycle we’re trying to defend against.
Even for well-funded enterprises, “more compute” isn’t a defensible decade-long strategy. For mid-market and smaller organizations — which together make up the majority of the economy and a meaningful share of critical supply chains — it isn’t even on the table. They cannot match attacker compute budgets. They never could. And we can’t leave them undefended, because their exposure becomes everyone else’s exposure the moment a single dependency, partner, or vendor in the chain gets compromised.
That’s the part the “AI fights AI” framing leaves out. Defense at the top of the market doesn’t actually work if it leaves the rest of the market exposed. The threat surface is collective. So is the answer.

The numbers that grounded the day
I’m not arguing the threat is exaggerated. The data from the sessions is loud:
- Non-human identities now outnumber humans 10 to 50x in most enterprises. Projected to widen by another 45x by 2027.
- 1,000+ AI-related regulations enacted globally since 2022.
- 74% of CIOs now rank AI governance as a top-three board concern.
- $4.9M average breach cost when AI-generated content or agents are involved.
This is real. The pressure is real. The regulatory clock is real. The technology is moving genuinely fast on both sides. None of this is in dispute.
The honest answer probably isn’t more compute. It’s three disciplines we’ll all need to get better at.
I don’t have a finished answer to the AI DDoS question. I’m not sure anyone does yet. But I do have a working hypothesis: if we can’t out-spend the adversary on raw compute, the defensive advantage has to come from discipline that compounds — for the largest enterprise and the mid-market firm both.
1. Govern what you already have before you buy more
A unified, jurisdiction-aware identity policy layer. Most enterprises are sitting on thousands of unmanaged non-human identities — AI agents, service accounts, API keys, RPA bots, CI/CD pipelines — all carrying real privileges, almost all undocumented. That is a free win for any attacker. No compute budget on the planet can outspend that gift.
Fragmentation is how audit gaps are born. One policy layer. Jurisdiction-aware. Enforced consistently across regions. That work is not glamorous. It is also non-optional.
2. Audit-ready visibility, not point-in-time audits
Continuous monitoring. Immutable logs. Mapped permissions. You may not out-compute an attacker, but you can shrink dwell time to seconds. The defensive posture that wins in an asymmetric fight isn’t bigger walls — it’s faster detection and faster response, with receipts regulators and auditors can rely on.
Point-in-time audits are theater for an environment where identities spawn child agents that inherit permissions and operate autonomously across regions you don’t control. The only audit posture that survives that environment is one that is always on.
3. Operational trust as a competitive advantage
Published policies. Third-party attestation. Transparent incident response. An AI governance function that sits above individual business units and is genuinely cross-functional.
The organizations that lead here set the standard. The ones that wait inherit one written by regulators. Operational trust is not a compliance line item — in an environment where the underlying technology is racing ahead of the rules, it becomes a durable competitive advantage. Customers, partners, and regulators are all evaluating AI governance maturity right now, whether they have a formal framework for it or not.
What we owe each other
Here’s the part of the conversation we don’t have often enough. If any of our 2026 security strategies — mine, yours, the most well-resourced enterprise’s — quietly assume we can simply out-compute the adversary, none of us have a strategy. We have a procurement plan with a burn rate the adversary will happily out-spend. And every mid-market and smaller organization downstream of us inherits whatever gap that leaves behind.
The arms race isn’t individually winnable. The discipline race might be — if we run it together.
That points to a few things the industry has to do collectively, not as a critique of any one player but as work we owe each other:
- Open-standard reference architectures for non-human identity governance — usable by an organization with two security engineers, not just a Fortune 100 SOC.
- Shared threat intel and detection signal across tiers, including the mid-market, so a compromised partner doesn’t become a free pivot into the rest of the supply chain.
- Affordable, audit-ready baseline tooling available below the enterprise price band. The math of “you can’t afford to be undefended” only works if the floor is reachable.
- Public-private coordination on the regulatory floor — so smaller organizations get a credible standard to operate to without having to invent it themselves.
That’s the part the “AI fights AI” slide doesn’t answer. It’s the part we still need to answer — vendors, analysts, CIOs, CISOs, regulators, all of us in the same room.
The most useful thing I took out of the room wasn’t on any of the slides. It was the shared honesty that none of us — vendor, analyst, CISO — had a satisfying answer yet. That kind of intellectual honesty is the start of a better playbook than any single talk could deliver on its own.
On the room itself
Genuine thanks to Natalia Klein and the team at Gartner C-Level Communities for orchestrating one of the most candid CIO and CISO rooms I’ve been in this year. The session quality was sharp, the agenda was tight, and the peer conversations — in the room, in the hallway, over coffee — were the kind that only happen when the format is built for practitioners rather than panels.
Good seeing Greg Taffet again — industry veteran CIO, sharper than most analysts in the room, and someone who has been asking the question that needs asking long enough to make the rest of us better at it.
Events like this are why I keep showing up: the value isn’t the keynote, it’s the density of candid conversation compressed into a single day. You learn more in eight hours of honest peer exchange than in eight weeks of analyst reports — because the reports describe the aspiration and the practitioners describe the reality.